The Internet
The Internet is a worldwide collection of interconnected networks (internetworks or internet for short). The figure shows one way to view the Internet as a collection of interconnected LANs and WANs. Some of the LAN examples are connected to each other through a WAN connection. WANs are then connected to each other. The red WAN connection lines represent all the varieties of ways we connect networks. WANs can connect through copper wires, fiber optic cables, and wireless transmissions

This is featured post 2 title
Replace these every slider sentences with your featured post descriptions.Go to Blogger edit html and find these sentences.Now replace these with your own descriptions.This theme is Bloggerized by Lasantha - Premiumbloggertemplates.com.

This is featured post 3 title
Replace these every slider sentences with your featured post descriptions.Go to Blogger edit html and find these sentences.Now replace these with your own descriptions.This theme is Bloggerized by Lasantha - Premiumbloggertemplates.com.

Wednesday, November 30, 2016
Security Solutions
A home network security implementation is usually rather basic. It is generally implemented on the connecting end devices, as well as at the point of connection to the Internet, and can even rely on contracted services from the ISP.
In contrast, the network security implementation for a corporate network usually consists of many components built into the network to monitor and filter traffic. Ideally, all components work together, which minimizes maintenance and improves security.
Network security components for a home or small office network should include, at a minimum:
- Antivirus and antispyware – These are used to protect end devices from becoming infected with malicious software.
- Firewall filtering – This is used to block unauthorized access to the network. This may include a host-based firewall system that is implemented to prevent unauthorized access to the end device, or a basic filtering service on the home router to prevent unauthorized access from the outside world into the network.
In addition to the above, larger networks and corporate networks often have other security requirements:
- Dedicated firewall systems – These are used to provide more advanced firewall capabilities that can filter large amounts of traffic with more granularity.
- Access control lists (ACL) – These are used to further filter access and traffic forwarding.
- Intrusion prevention systems (IPS) – These are used to identify fast-spreading threats, such as zero-day or zero-hour attacks.
- Virtual private networks (VPN) – These are used to provide secure access to remote workers.
Network security requirements must take into account the network environment, as well as the various applications, and computing requirements. Both home environments and businesses must be able to secure their data while still allowing for the quality of service that is expected of each technology. Additionally, the security solution implemented must be adaptable to the growing and changing trends of the network.
The study of network security threats and mitigation techniques starts with a clear understanding of the underlying switching and routing infrastructure used to organize network services.
Security Threats
Securing a network involves protocols, technologies, devices, tools, and techniques to secure data and mitigate threats. Threat vectors may be external or internal. Many external network security threats today are spread over the Internet.
The most common external threats to networks include:
- Viruses, worms, and Trojan horses - malicious software and arbitrary code running on a user device
- Spyware and adware - software installed on a user device that secretly collects information about the user
- Zero-day attacks, also called zero-hour attacks - an attack that occurs on the first day that a vulnerability becomes known
- Hacker attacks - an attack by a knowledgeable person to user devices or network resources
- Denial of service attacks - attacks designed to slow or crash applications and processes on a network device
- Data interception and theft - an attack to capture private information from an organization’s network
- Identity theft - an attack to steal the login credentials of a user in order to access private data
It is equally important to consider internal threats. There have been many studies that show that the most common data breaches happen because of internal users of the network. This can be attributed to lost or stolen devices, accidental misuse by employees, and in the business environment, even malicious employees. With the evolving BYOD strategies, corporate data is much more vulnerable. Therefore, when developing a security policy, it is important to address both external and internal security threats.
Wireless Broadband
Wireless Internet Service Provider (WISP)
Wireless Internet Service Provider (WISP) is an ISP that connects subscribers to a designated access point or hot spot using similar wireless technologies found in home wireless local area networks (WLANs). WISPs are more commonly found in rural environments where DSL or cable services are not available.
Although a separate transmission tower may be installed for the antenna, it is common that the antenna is attached to an existing elevated structure, such as a water tower or a radio tower. A small dish or antenna is installed on the subscriber’s roof in range of the WISP transmitter. The subscriber’s access unit is connected to the wired network inside the home. From the perspective of the home user, the setup is not much different than DSL or cable service. The main difference is that the connection from the home to the ISP is wireless instead of a physical cable.
Wireless Broadband Service
Another wireless solution for the home and small businesses is wireless broadband, as shown in the figure. This uses the same cellular technology used to access the Internet with a smart phone or tablet. An antenna is installed outside the house providing either wireless or wired connectivity for devices in the home. In many areas, home wireless broadband is competing directly with DSL and cable services.
Sunday, November 20, 2016
Technology Trends in the Home
The newest home trends include ‘smart home technology’. Smart home technology is technology that is integrated into every-day appliances allowing them to interconnect with other devices, making them more ‘smart’ or automated. For example, imagine being able to prepare a dish and place it in the oven for cooking prior to leaving the house for the day. Imagine if the oven was ‘aware’ of the dish it was cooking and was connected to your ‘calendar of events’ so that it could determine what time you should be available to eat, and adjust start times and length of cooking accordingly. It could even adjust cooking times and temperatures based on changes in schedule. Additionally, a smartphone or tablet connection allows the user the ability to connect to the oven directly, to make any desired adjustments. When the dish is “available”, the oven sends an alert message to a specified end user device that the dish is done and warming.
This scenario is not long off. In fact, smart home technology is currently being developed for all rooms within a house. Smart home technology will become more of a reality as home networking and high-speed Internet technology becomes more widespread. New home networking technologies are being developed daily to meet these types of growing technology needs.
Cloud Computing
For businesses, Cloud computing extends IT's capabilities without requiring investment in new infrastructure, training new personnel, or licensing new software. These services are available on demand and delivered economically to any device anywhere in the world without compromising security or function.
There are four primary types of Clouds, as shown in the figure: Public Clouds, Private Clouds, Hybrid Clouds, and Custom Clouds. Click each Cloud to learn more.
Cloud computing is possible because of data centers. A data center is a facility used to house computer systems and associated components. A data center can occupy one room of a building, one or more floors, or an entire building. Data centers are typically very expensive to build and maintain. For this reason, only large organizations use privately built data centers to house their data and provide services to users. Smaller organizations that cannot afford to maintain their own private data center can reduce the overall cost of ownership by leasing server and storage services from a larger data center organization in the Cloud.
Video Communication
Video conferencing is a powerful tool for communicating with others at a distance, both locally and globally. Video is becoming a critical requirement for effective collaboration as organizations extend across geographic and cultural boundaries. Click Play in the figure to view how TelePresence can be incorporated into everyday life and business.
Click here to read the transcript of this video.
Online Collaboration
For businesses, collaboration is a critical and strategic priority that organizations are using to remain competitive. Collaboration is also a priority in education. Students need to collaborate to assist each other in learning, to develop team skills used in the work force, and to work together on team-based projects.
Bring Your Own Device
BYOD is about end users having the freedom to use personal tools to access information and communicate across a business or campus network. With the growth of consumer devices, and the related drop in cost, employees and students can be expected to have some of the most advanced computing and networking tools for personal use. These personal tools include laptops, netbooks, tablets, smartphones, and e-readers. These can be devices purchased by the company or school, purchased by the individual, or both.
BYOD means any device, with any ownership, used anywhere. For example, in the past, a student who needed to access the campus network or the Internet had to use one of the school’s computers. These devices were typically limited and seen as tools only for work done in the classroom or in the library. Extended connectivity through mobile and remote access to the campus network gives students tremendous flexibility and more learning opportunities for the student.
.
New Trends
 As new technologies and end user devices come to market, businesses and consumers must continue to adjust to this ever-changing environment. The role of the network is transforming to enable the connections between people, devices, and information. There are several new networking trends that will effect organizations and consumers. Some of the top trends include:
As new technologies and end user devices come to market, businesses and consumers must continue to adjust to this ever-changing environment. The role of the network is transforming to enable the connections between people, devices, and information. There are several new networking trends that will effect organizations and consumers. Some of the top trends include:- Bring Your Own Device (BYOD)
- Online collaboration
- Video communications
- Cloud computing
Security
Securing a network infrastructure includes the physical securing of devices that provide network connectivity, and preventing unauthorized access to the management software that resides on them, as shown in Figure 1.
Information security refers to protecting the information contained within the packets being transmitted over the network and the information stored on network attached devices. In order to achieve the goals of network security, there are three primary requirements, as shown in Figure 2:
- Confidentiality - Data confidentiality means that only the intended and authorized recipients can access and read data.
- Integrity - Data integrity means having the assurance that the information has not been altered in transmission, from origin to destination.
- Availability - Data availability means having the assurance of timely and reliable access to data services for authorized users.
Quality of Service
Congestion occurs when the demand for bandwidth exceeds the amount available. Network bandwidth is measured in the number of bits that can be transmitted in a single second, or bits per second (bps). When simultaneous communications are attempted across the network, the demand for network bandwidth can exceed its availability, creating network congestion.
When the volume of traffic is greater than what can be transported across the network, devices queue, or hold, the packets in memory until resources become available to transmit them. In the figure, one user is requesting a web page and another is on a phone call. With a QoS policy in place, the router can manage the flow of data and voice traffic, giving priority to voice communications if the network experiences congestion.
To learn more about QoS as a requirement for reliable networks, refer to the Appendix for this chapter.
Scalability
 A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users. The figure shows how a new network can be easily added to an existing network. In addition, networks are scalable because the designers follow accepted standards and protocols. This allows software and hardware vendors to focus on improving products and services without worrying about designing a new set of rules for operating within the network.
A scalable network can expand quickly to support new users and applications without impacting the performance of the service being delivered to existing users. The figure shows how a new network can be easily added to an existing network. In addition, networks are scalable because the designers follow accepted standards and protocols. This allows software and hardware vendors to focus on improving products and services without worrying about designing a new set of rules for operating within the network. To learn more about scalability as a requirement for reliable networks, refer to the Appendix for this chapter.
Fault Tolerance
One way reliable networks provide redundancy is by implementing a packet-switched network. Packet switching splits traffic into packets that are routed over a shared network. A single message, such as an email or a video stream, is broken into multiple message blocks, called packets. Each packet has the necessary addressing information of the source and destination of the message. The routers within the network switch the packets based on the condition of the network at that moment. This means that all the packets in a single message could take very different paths to the destination. In the figure, the user is not aware and is unaffected by the router dynamically changing the route when a link fails.
This is not the case in circuit-switched networks traditionally used for voice communications. A circuit-switched network is one that establishes a dedicated circuit between the source and destination before the users may communicate. If the call is unexpectedly terminated, the users must initiate a new connection.
To learn more about packet-switched and circuit-switched networks, refer to the Appendix for this chapter.
Network Architecture
As networks evolve, we are discovering that there are four basic characteristics that the underlying architectures need to address in order to meet user expectations:
- Fault Tolerance
- Scalability
- Quality of Service (QoS)
- Security
Lab – Researching Converged Network Services
- Part 1: Survey Your Understanding of Convergence
- Part 2: Research ISPs Offering Converged Services
- Part 3: Research Local ISPs Offering Converged Services
- Part 4: Select Best Local ISP Converged Service
- Part 5: Research Local Company or Public Institution Using Convergence Technologies
.
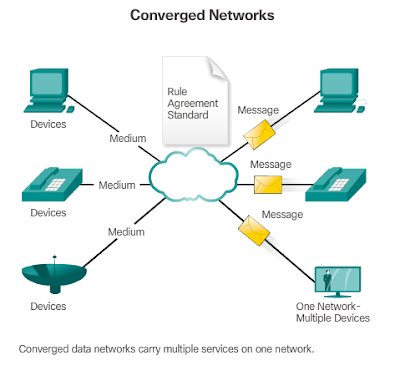
The Converging Network
Traditional Separate Networks
Packet Tracer - Network Representation
Packet Tracer - Network Representation Instructions
Packet Tracer - Network Representation - PKA
Packet Tracer - Help and Navigation Tips
Packet Tracer – Help and Navigation Tips Instructions
Packet Tracer – Help and Navigation Tips - PKA
Businesses Internet Connections
 Corporate connection options differ from home user options. Businesses may require higher bandwidth, dedicated bandwidth, and managed services. Connection options available differ depending on the type of service providers located nearby.
Corporate connection options differ from home user options. Businesses may require higher bandwidth, dedicated bandwidth, and managed services. Connection options available differ depending on the type of service providers located nearby. The figure illustrates common connection options for businesses:
- Dedicated Leased Line - Leased lines are actually reserved circuits within the service provider’s network that connect geographically separated offices for private voice and/or data networking. The circuits are typically rented at a monthly or yearly rate. They can be expensive.
- Ethernet WAN - Ethernet WANs extend LAN access technology into the WAN. Ethernet is a LAN technology you will learn about in a later chapter. The benefits of Ethernet are now being extended into the WAN.
- DSL - Business DSL is available in various formats. A popular choice is Symmetric Digital Subscriber Lines (SDSL) which is similar to the consumer version of DSL, but provides uploads and downloads at the same speeds.
- Satellite - Similar to small office and home office users, satellite service can provide a connection when a wired solution is not available.
Home and Small Office Internet Connections
 The figure illustrates common connection options for small office and home office users:
The figure illustrates common connection options for small office and home office users:- Cable - Typically offered by cable television service providers, the Internet data signal is carried on the same cable that delivers cable television. It provides a high bandwidth, always on, connection to the Internet.
- DSL - Digital Subscriber Lines provide a high bandwidth, always on, connection to the Internet. DSL runs over a telephone line. In general, small office and home office users connect using Asymmetrical DSL (ADSL), which means that the download speed is faster than the upload speed.
- Cellular - Cellular Internet access uses a cell phone network to connect. Wherever you can get a cellular signal, you can get cellular Internet access. Performance will be limited by the capabilities of the phone and the cell tower to which it is connected.
- Satellite - The availability of satellite Internet access is a real benefit in those areas that would otherwise have no Internet connectivity at all. Satellite dishes require a clear line of sight to the satellite.
- Dial-up Telephone - An inexpensive option that uses any phone line and a modem. The low bandwidth provided by a dial-up modem connection is usually not sufficient for large data transfer, although it is useful for mobile access while traveling.
The choice of connection varies depending on geographical location and service provider availability.
Internet Access Technologies
Home users, teleworkers (remote workers), and small offices typically require a connection to an Internet Service Provider (ISP) to access the Internet. Connection options vary greatly between ISP and geographical location. However, popular choices include broadband cable, broadband digital subscriber line (DSL), wireless WANs, and mobile services.
Organizations typically require access to other corporate sites and the Internet. Fast connections are required to support business services including IP phones, video conferencing, and data center storage.
Business-class interconnections are usually provided by service providers (SP). Popular business-class services include business DSL, leased lines, and Metro Ethernet.
Intranets and Extranets
- Intranet
- Extranet
An organization may use an extranet to provide secure and safe access to individuals who work for a different organization, but require access to the organization’s data. Examples of extranets include:
- A company that is providing access to outside suppliers and contractors.
- A hospital that is providing a booking system to doctors so they can make appointments for their patients.
- A local office of education that is providing budget and personnel information to the schools in its district.


 3:50 PM
3:50 PM
 bestmongol2
bestmongol2